TL;DR
Why Digital Transformation Fails in Manufacturing (and How to Fix It) — this comprehensive guide provides engineers and system integrators with practical, data-driven insights into industrial digital transformation strategy. Covering key standards (Industry 4.0, IEC 62443, ISA-95, RAMI 4.0), technical specifications, and deployment best practices, this article helps decision-makers select and implement the right solutions for their thought leadership requirements.
Industry Overview
The industrial digital transformation strategy landscape is evolving rapidly as organizations modernize their operational technology infrastructure. Engineers face growing challenges: OT-IT convergence, legacy infrastructure, skills gap, cybersecurity, ROI justification. This guide addresses these challenges with practical solutions backed by technical specifications and real-world deployment data.
Understanding the requirements starts with the standards that govern this domain. Key standards include Industry 4.0, IEC 62443, ISA-95, RAMI 4.0, each addressing specific aspects of system design, security, and interoperability.
| Standard | Focus Area | Relevance to Thought Leadership |
|---|---|---|
| Industry 4.0 | Primary compliance | Foundation for system design |
| IEC 62443 | Cybersecurity | Network security architecture |
| IEEE 802.3 | Ethernet | Physical layer requirements |
The Challenge
Organizations deploying industrial digital transformation strategy solutions encounter several technical obstacles:
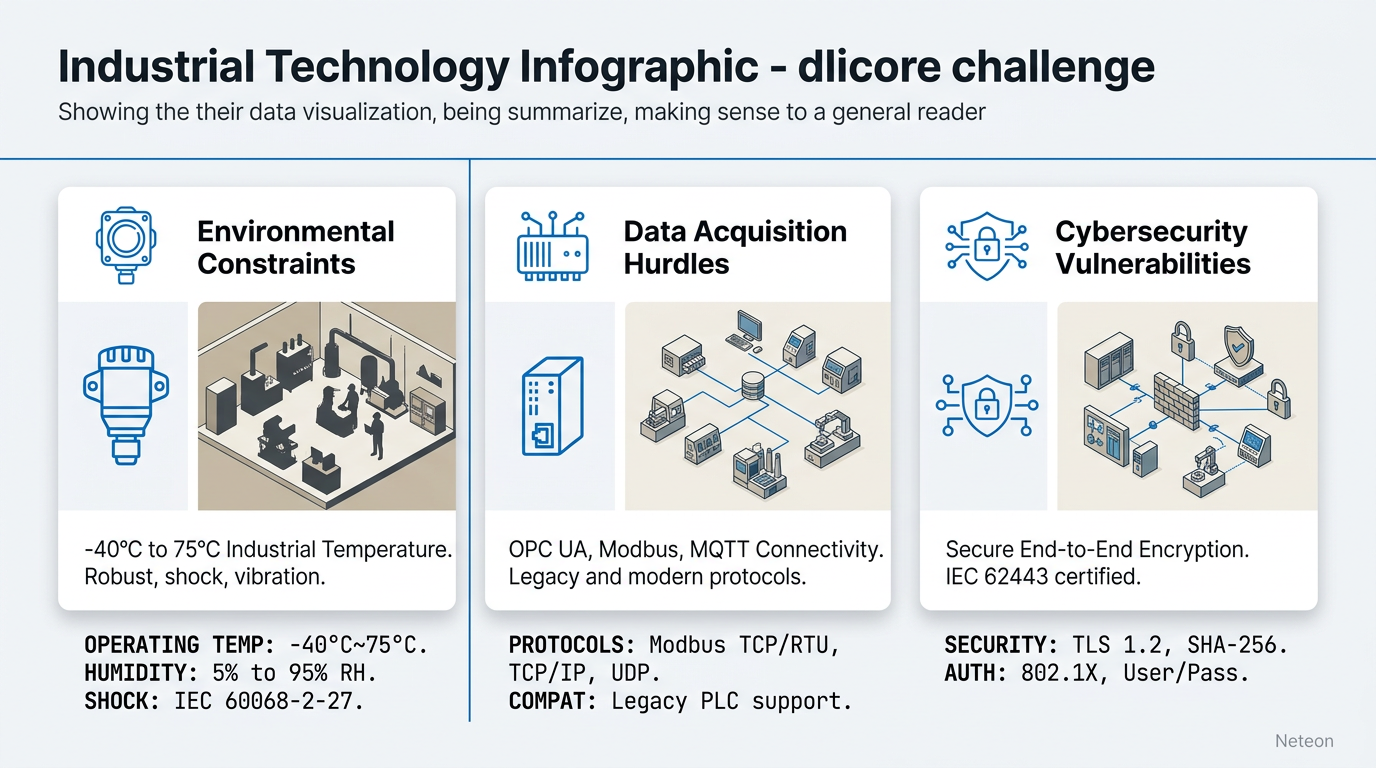
Environmental constraints — Industrial environments impose requirements far beyond commercial specifications. Temperature extremes (-40°C to 75°C), vibration, EMI, dust, and moisture demand purpose-built equipment rated for these conditions.
Protocol diversity — Multiple communication protocols must coexist on the same network infrastructure. Legacy serial protocols (Modbus RTU, DNP3) need to communicate with modern Ethernet-based systems, requiring protocol gateways and careful network design.
Availability requirements — Critical infrastructure demands 99.999% uptime, translating to less than 5.26 minutes of downtime per year. This requires redundant network paths with sub-second failover capabilities.
| Requirement | Standard Solution | Industrial Solution |
|---|---|---|
| Temperature | 0-40°C (commercial) | -40 to 75°C (wide-temp) |
| Redundancy | STP (30-50 sec) | Turbo Ring (<20ms) |
| Protocols | TCP/IP only | Multi-protocol (Modbus, DNP3, OPC UA) |
| Lifecycle | 3-5 years | 10-15+ years |
| Security | IT-grade | IEC 62443 OT-grade |
The Solution
Effective solutions for industrial digital transformation strategy combine purpose-built hardware with proper network architecture:
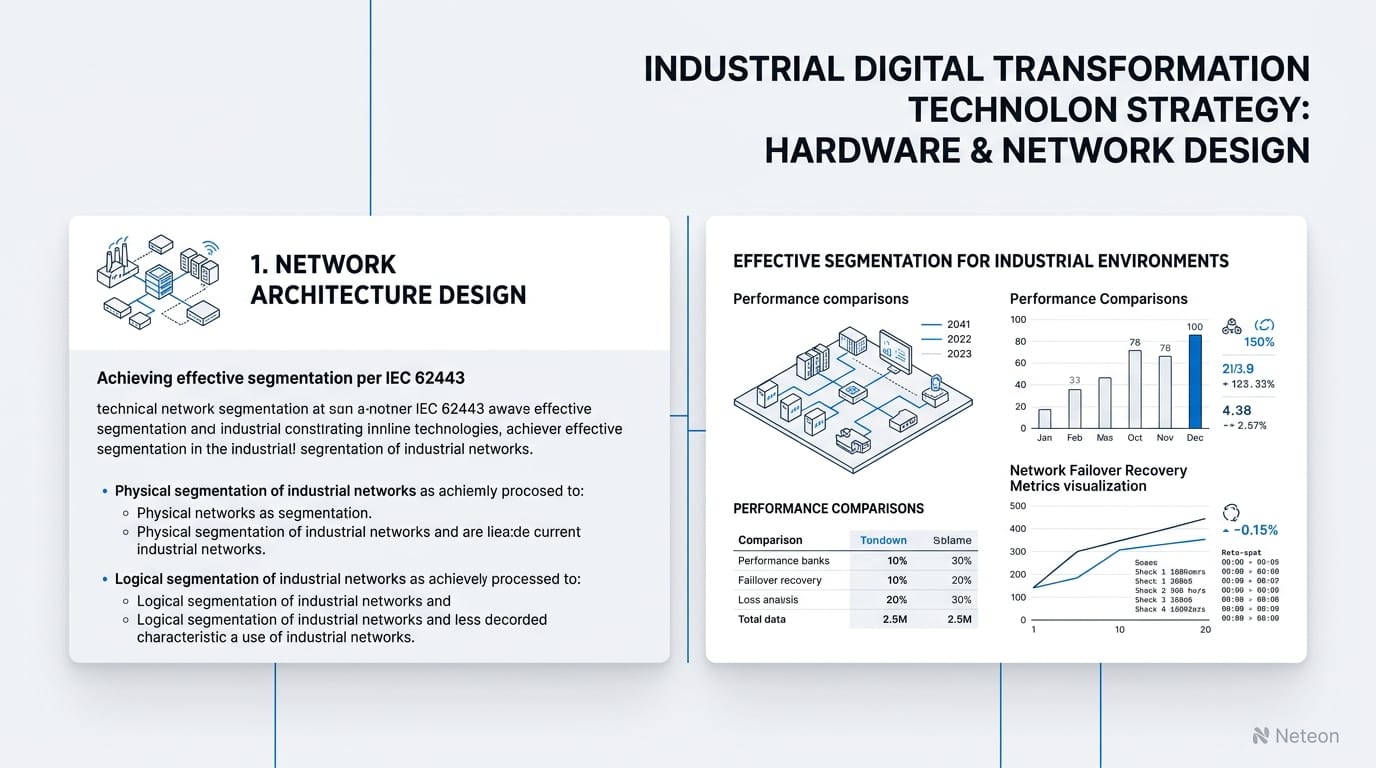
1. Network Architecture Design
Implement zone-and-conduit architecture per IEC 62443. Separate critical control systems, monitoring, and enterprise traffic using VLAN segmentation on managed industrial switches.
| Zone | Function | Security Level | Networking |
|---|---|---|---|
| Critical Control | Safety, protection | SL 3 | Dedicated VLAN, PRP/HSR |
| Process Control | SCADA, DCS, PLC | SL 2-3 | Managed switches, Turbo Ring |
| Monitoring | Historians, analytics | SL 2 | Standard managed Ethernet |
| Enterprise | IT, office, remote | SL 1-2 | IT switches, DMZ boundary |
2. Equipment Selection
Select industrial networking equipment rated for the deployment environment. Neteon industrial networking solutions portfolio provide the environmental ratings, protocol support, and redundancy capabilities required for reliable operation.
| Feature | Specification | Benefit |
|---|---|---|
| Operating Temp | -40°C to 75°C | Reliable operation in extreme conditions |
| Redundancy | Turbo Ring <20ms | Transparent failover for critical systems |
| Security | IEC 62443-4-2 SL2+ | Compliant cybersecurity posture |
| Management | SNMPv3, HTTPS, SSH | Secure remote monitoring and configuration |
3. Implementation Best Practices
| Phase | Duration | Activities |
|---|---|---|
| Design | 2-4 weeks | Network topology, equipment specification, VLAN plan |
| Deploy | 4-8 weeks | Equipment installation, configuration, cable routing |
| Commission | 1-2 weeks | Testing, redundancy verification, documentation |
| Optimize | Ongoing | Monitoring, firmware updates, capacity planning |
Cybersecurity & Reliability
| Security Layer | Implementation | Standard Compliance |
|---|---|---|
| Network Segmentation | VLAN + firewall zones | IEC 62443-3-3 FR5 |
| Access Control | 802.1X, RADIUS, RBAC | IEC 62443-3-3 FR1-2 |
| Monitoring | SNMP, syslog, MXview One | IEC 62443-3-3 FR6 |
| Device Hardening | Disable unused ports/services | IEC 62443-4-2 |
| Redundancy | Turbo Ring, dual power | Availability targets |
Reliability specifications: - MTBF: >500,000 hours for industrial switches - Failover: <20ms with Turbo Ring, 0ms with PRP/HSR - Power: Dual redundant DC inputs (12-48VDC) - Environmental: IEC 60068-2-6 vibration, IEC 60068-2-27 shock
Related Products
Product cards auto-generated by shopmoxa_scraper.py
Conclusion
Successful industrial digital transformation strategy deployments require purpose-built industrial networking equipment, proper network architecture, and adherence to relevant standards. Starting with a thorough requirements analysis and implementing zone-based security architecture provides a solid foundation for reliable, secure operations. For technical specifications, network design assistance, or application engineering support, contact Neteon's engineering team or explore our industrial networking solutions.
Frequently Asked Questions
Q: What standards should I follow for thought leadership networking? A: Key standards include Industry 4.0, IEC 62443, ISA-95, RAMI 4.0. IEC 62443 provides the cybersecurity framework, while domain-specific standards address environmental and functional requirements.
Q: What is the typical ROI timeline for industrial networking upgrades? A: Most organizations achieve ROI within 12-18 months through reduced downtime (a single hour of unplanned downtime costs $10,000-$100,000+ depending on the operation), improved remote diagnostics, and lower maintenance costs.
Q: Can existing legacy equipment be integrated with modern industrial networks? A: Yes. Protocol gateways (like Moxa MGate Series) convert legacy serial protocols (Modbus RTU, DNP3) to Ethernet-based communication. This allows gradual migration without replacing all field devices simultaneously.
Q: How do I ensure cybersecurity for my thought leadership network? A: Implement IEC 62443 zone-and-conduit architecture with industrial firewalls at zone boundaries, enable 802.1X port authentication on managed switches, deploy network monitoring, and maintain a regular firmware update schedule.
Q: What redundancy protocol should I choose? A: For most industrial applications, Turbo Ring (<20ms recovery, up to 250 switches) provides the optimal balance of speed and scalability. For safety-critical systems (substations, SIL-rated), use PRP/HSR for zero-loss redundancy.



