TLDR: Operational Technology (OT) cybersecurity protects industrial control systems, SCADA networks, and critical infrastructure from cyber threats. Unlike IT security, OT environments prioritize availability and safety over confidentiality. This guide covers the core differences between IT and OT security, key threat vectors targeting industrial networks, the IEC 62443 framework, and practical defense-in-depth strategies using industrial-grade firewalls, network segmentation, and intrusion prevention.
What Is OT Cybersecurity?
OT cybersecurity is the practice of protecting industrial control systems (ICS), supervisory control and data acquisition (SCADA) networks, distributed control systems (DCS), and programmable logic controllers (PLCs) from unauthorized access, disruption, or manipulation.
Industrial networks now connect thousands of devices across manufacturing floors, power substations, water treatment plants, and transportation systems. The convergence of IT and OT networks has created new attack surfaces. According to CISA, ransomware incidents targeting OT environments increased by 87% between 2023 and 2025. The average cost of an OT-related breach in critical infrastructure exceeds $4.7 million.
The core challenge is straightforward. Legacy OT devices were designed for reliability in isolated networks, not for security in connected environments. Many industrial protocols like Modbus, DNP3, and PROFINET lack built-in authentication or encryption. Retrofitting security without disrupting 24/7 operations requires a fundamentally different approach than traditional IT security.
Why IT Security Approaches Fail in OT Environments
Engineers managing industrial networks cannot simply deploy enterprise firewalls and antivirus solutions. The operating requirements are fundamentally different.
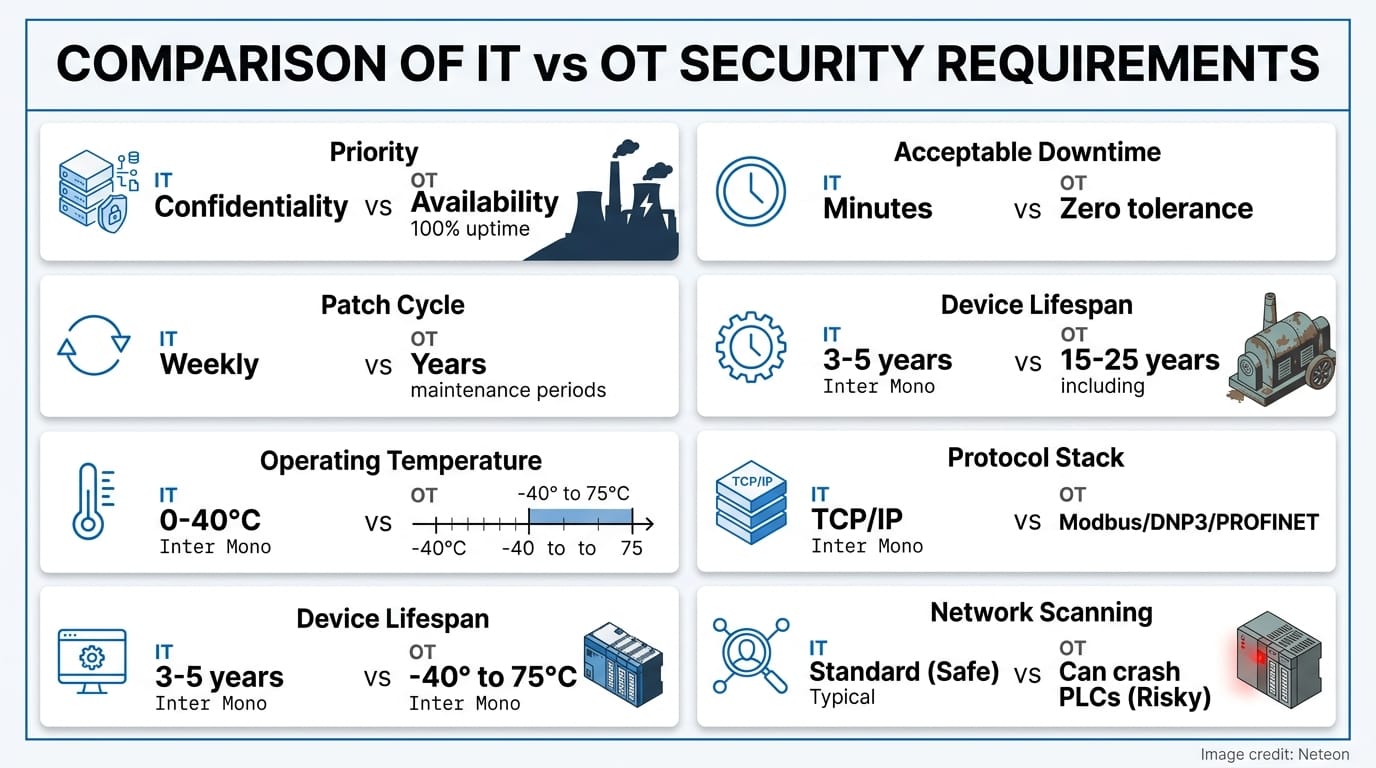
| Requirement | IT Environment | OT Environment |
|---|---|---|
| Top Priority | Confidentiality (CIA triad) | Availability and Safety |
| Acceptable Downtime | Minutes to hours (planned maintenance) | Zero tolerance — 99.999% uptime required |
| Patch Cycle | Weekly/monthly updates | Years between updates; vendor certification required |
| Device Lifespan | 3-5 years | 15-25 years |
| Operating Temperature | 0°C to 40°C (climate-controlled) | -40°C to 75°C (harsh industrial environments) |
| Protocol Stack | TCP/IP, HTTP, TLS | Modbus TCP, DNP3, EtherNet/IP, OPC UA, PROFINET |
| Network Scanning | Standard practice | Can crash PLCs and halt production |
Standard vulnerability scanners can trigger faults in legacy PLCs. Automatic patching can take a production line offline. Passive traffic analysis is often the only safe method for discovering OT assets.
Top Threat Vectors Targeting Industrial Networks
Industrial networks face specific attack patterns that exploit OT-unique weaknesses.
1. Ransomware targeting HMI and SCADA systems. Attackers pivot from IT networks into OT zones through flat network architectures lacking proper segmentation. The 2021 Colonial Pipeline attack demonstrated how a single compromised VPN credential can shut down critical infrastructure.
2. Protocol exploitation. Modbus TCP transmits commands in cleartext without authentication. An attacker on the network can issue unauthorized write commands to PLCs. DNP3 Secure Authentication (SA) adds HMAC-based validation, but adoption remains below 15% industry-wide.
3. Supply chain compromise. Firmware updates from compromised vendors can introduce backdoors into industrial switches and gateways. IEC 62443-4-1 mandates secure development lifecycle (SDL) practices for component suppliers.
4. Unauthorized remote access. Maintenance VPNs with shared credentials create persistent entry points. The shift to cloud-connected IIoT devices expands the attack surface further.
Building Defense-in-Depth for Industrial Networks
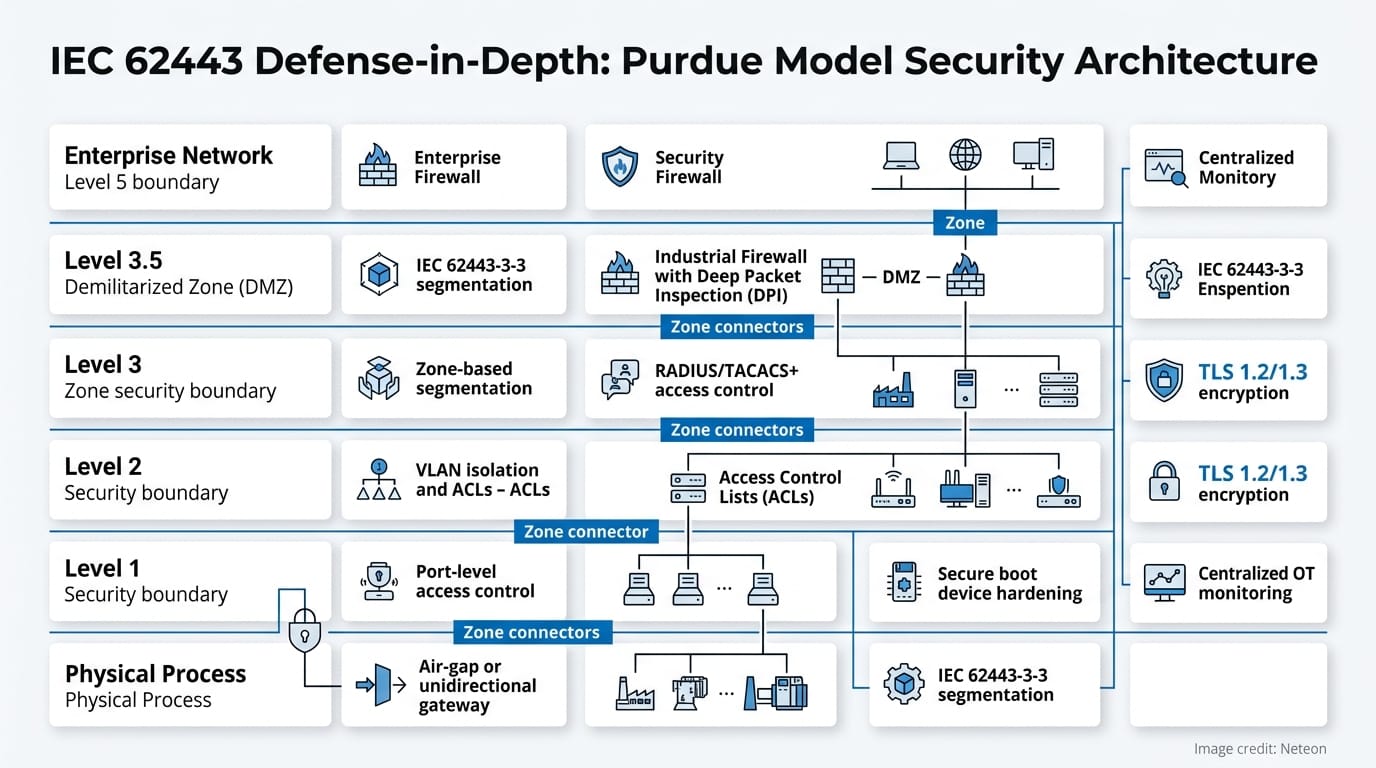
The IEC 62443 framework provides the most comprehensive blueprint for OT cybersecurity. It defines security levels (SL1-SL4) and organizes defenses into zones and conduits.
Step 1: Network Segmentation and Zone Architecture
The Purdue Model divides industrial networks into hierarchical levels. Each level boundary requires a security conduit — an industrial secure router with deep packet inspection (DPI) for OT protocols.
| Purdue Level | Function | Security Boundary |
|---|---|---|
| Level 5 | Enterprise Network (ERP, email) | Enterprise firewall |
| Level 3.5 | DMZ (historian, patch server) | Industrial firewall with DPI |
| Level 3 | Site Operations (SCADA server) | Zone-based segmentation |
| Level 2 | Area Control (HMI, engineering workstations) | VLAN isolation + ACLs |
| Level 1 | Basic Control (PLC, RTU) | Port-level access control |
| Level 0 | Physical Process (sensors, actuators) | Air-gap or unidirectional gateway |
Effective segmentation reduces the blast radius of a breach. The Moxa EDR-G9010 Series provides zone-based firewalling with Modbus DPI, allowing engineers to create granular rules such as "allow Modbus read commands from HMI subnet, block all write commands from Level 3+."
Step 2: Industrial Intrusion Prevention
Traditional IT IPS systems generate excessive false positives on OT protocols because they lack industrial protocol awareness. An OT-specific IPS must understand the semantics of Modbus function codes, DNP3 objects, and EtherNet/IP CIP services.
| Security Feature | Enterprise IPS | OT-Specific IPS (e.g., Moxa IEC Series) |
|---|---|---|
| Protocol Coverage | HTTP, SMTP, DNS | Modbus, DNP3, EtherNet/IP, OPC UA |
| False Positive Rate | 5-15% on OT traffic | <1% with industrial protocol signatures |
| Deployment Impact | Requires agent installation | Inline or passive monitoring — zero agent |
| Operating Temp | 0°C to 40°C | -40°C to 75°C |
| Management | SIEM integration | MXsecurity centralized OT security dashboard |
Step 3: Continuous Monitoring and Asset Visibility
You cannot protect what you cannot see. A 2025 SANS ICS survey found that 62% of industrial organizations lack a complete inventory of their OT assets.
MXview network management software provides real-time topology visualization, automatic device discovery, and event correlation across industrial networks. Combined with MXsecurity for centralized threat management, engineers gain a single pane of glass covering both network health and security posture.
Cybersecurity and Reliability Working Together
Security controls must not compromise system availability. Industrial-grade security-hardened network devices are built to maintain both.
| Security Layer | Implementation | Standard Compliance |
|---|---|---|
| Network Segmentation | Zone-based firewalling with OT protocol DPI | IEC 62443-3-3 |
| Access Control | RADIUS/TACACS+ with role-based policies | IEC 62443-4-2 SL2-SL3 |
| Device Hardening | Secure boot, signed firmware, disabled unused ports | NIST SP 800-82 |
| Firmware Integrity | Cryptographic code signing and update verification | IEC 62443-4-1 SDL |
| Encryption | TLS 1.2/1.3 for management traffic; selective for control | IEC 62351 |
| Monitoring | Centralized OT security dashboard with anomaly detection | NERC CIP-005/007 |
Moxa's security-hardened devices achieve IEC 62443-4-2 certification at Security Level 2, with features including secure boot, encrypted configuration backup, and automatic session timeout.
Related Products
Recommended Products from ShopMoxa
Conclusion
OT cybersecurity is not an IT project with industrial hardware. It requires purpose-built strategies that prioritize availability, understand industrial protocols, and respect the operational constraints of 24/7 production environments. The IEC 62443 framework, combined with industrial-grade firewalls, protocol-aware intrusion prevention, and centralized monitoring, provides a proven path to securing converging IT/OT networks.
For technical specifications, network design assistance, or application engineering support, contact our engineering team at shopmoxa.neteon.net/contact. Visit shopmoxa.neteon.net for detailed datasheets, configuration guides, and network design tools.
Frequently Asked Questions
Q: What is the difference between OT cybersecurity and IT cybersecurity? A: IT cybersecurity prioritizes data confidentiality, while OT cybersecurity prioritizes system availability and physical safety. OT environments run legacy devices with 15-25 year lifespans, use industrial protocols like Modbus and DNP3 that lack built-in encryption, and cannot tolerate downtime for patching. Standard IT tools like vulnerability scanners can crash PLCs and halt production.
Q: What is IEC 62443 and why does it matter for industrial networks? A: IEC 62443 is the international standard for industrial automation and control system (IACS) cybersecurity. It defines security levels (SL1-SL4), organizes networks into zones and conduits, and provides requirements for both component manufacturers and system integrators. Compliance demonstrates that security controls meet recognized industrial benchmarks.
Q: How does network segmentation protect OT environments? A: Network segmentation divides the industrial network into isolated zones based on the Purdue Model, with security conduits controlling traffic between levels. If an attacker compromises the enterprise network, zone-based firewalling with deep packet inspection prevents lateral movement into control system layers. This reduces the blast radius of any breach.
Q: Can legacy industrial devices be secured without replacing them? A: Yes. Industrial secure routers like the Moxa EDR-G9010 Series can be deployed at zone boundaries to enforce access control, protocol filtering, and deep packet inspection around legacy devices. This approach provides security without requiring firmware updates or replacement of equipment that may lack native security features.
Q: What is deep packet inspection for OT protocols? A: OT-specific deep packet inspection (DPI) analyzes the content of industrial protocol traffic — not just packet headers. For example, DPI can inspect Modbus function codes to allow read commands from HMI subnets while blocking unauthorized write commands. This provides granular control that standard IT firewalls cannot achieve with proprietary industrial protocols.









