TL;DR
The NIST Cybersecurity Framework (CSF) 2.0 provides a structured approach to securing operational technology environments. This implementation roadmap translates NIST's five core functions into actionable steps for industrial networks, with specific tool recommendations, timeline estimates, and compliance milestones for OT engineers and CISOs.
Why NIST CSF for OT?
The NIST Cybersecurity Framework has become the de facto standard for organizations seeking to improve their cybersecurity posture. With the CSF 2.0 update (released February 2024), NIST expanded its scope explicitly to include operational technology and critical infrastructure. Unlike prescriptive standards like IEC 62443, NIST CSF provides a flexible, risk-based framework that organizations can adapt to their specific OT environments.
For industrial operators, NIST CSF serves as a bridge between executive-level risk management and engineering-level implementation. It provides common language for IT and OT teams to align on security priorities.
| Framework | Focus | Prescriptive Level | Best For |
|---|---|---|---|
| NIST CSF 2.0 | Risk management | Flexible, outcome-based | Organization-wide strategy |
| IEC 62443 | IACS security | Highly prescriptive | Technical implementation |
| NIST SP 800-82 | ICS security | Detailed guidance | OT-specific controls |
| NERC CIP | Power grid | Mandatory compliance | Electric utilities |
The Five Core Functions Applied to OT
Function 1: Identify
Goal: Build complete visibility of all OT assets, network connections, and data flows.
The biggest gap in most OT environments is visibility. You cannot protect what you cannot see. Unlike IT, where CMDB tools track assets automatically, OT devices often lack agents and use proprietary protocols invisible to standard discovery tools.
Key activities: - Passive network discovery using tools like MXview One — scans without disrupting PLCs - Build OT asset inventory: PLCs, RTUs, HMIs, switches, gateways with firmware versions - Map network topology and data flows between Purdue Model levels - Classify assets by criticality (safety, production, monitoring)
| Asset Category | Discovery Method | Typical Count (medium plant) |
|---|---|---|
| Managed Switches | SNMP/LLDP discovery | 50-200 |
| PLCs/RTUs | Passive protocol analysis | 100-500 |
| HMIs/Workstations | Network scan + agent | 20-50 |
| IoT Sensors | DHCP/ARP monitoring | 200-1,000+ |
| Unmanaged Devices | MAC address detection | 50-300 |
Function 2: Protect
Goal: Implement safeguards to limit the impact of potential security events.
Protection in OT focuses on network segmentation, access control, and protocol filtering — not endpoint agents that could impact real-time performance.
Key activities: - Implement IEC 62443 zone-and-conduit architecture - Deploy industrial firewalls (Moxa EDR-G9010) at zone boundaries - Configure VLAN segmentation on managed industrial switches - Enable 802.1X port authentication where supported - Establish secure remote access via industrial VPN with MFA
Function 3: Detect
Goal: Identify cybersecurity events in real-time through continuous monitoring.
Detection in OT requires protocol-aware monitoring that understands the difference between a legitimate Modbus write command and an unauthorized one.
Key activities: - Deploy OT-aware network monitoring with protocol analysis - Configure alert thresholds for anomalous OT traffic patterns - Integrate OT monitoring with enterprise SIEM for correlated visibility - Establish baseline network behavior profiles for each zone
Function 4: Respond
Goal: Contain and mitigate detected security incidents without disrupting operations.
OT incident response must prioritize operational continuity. Unlike IT, where you might isolate a compromised server immediately, shutting down an OT system could cause physical safety hazards.
Key activities: - Develop OT-specific incident response procedures - Pre-configure firewall rules for rapid zone isolation - Establish communication protocols between IT SOC and OT operations - Conduct tabletop exercises with both IT and OT personnel
Function 5: Recover
Goal: Restore affected OT systems to normal operation with validated integrity.
Key activities: - Maintain offline backups of PLC programs and HMI configurations - Test recovery procedures during planned maintenance windows - Document validated recovery time objectives (RTOs) per system criticality - Implement network redundancy with Turbo Ring for <50ms failover
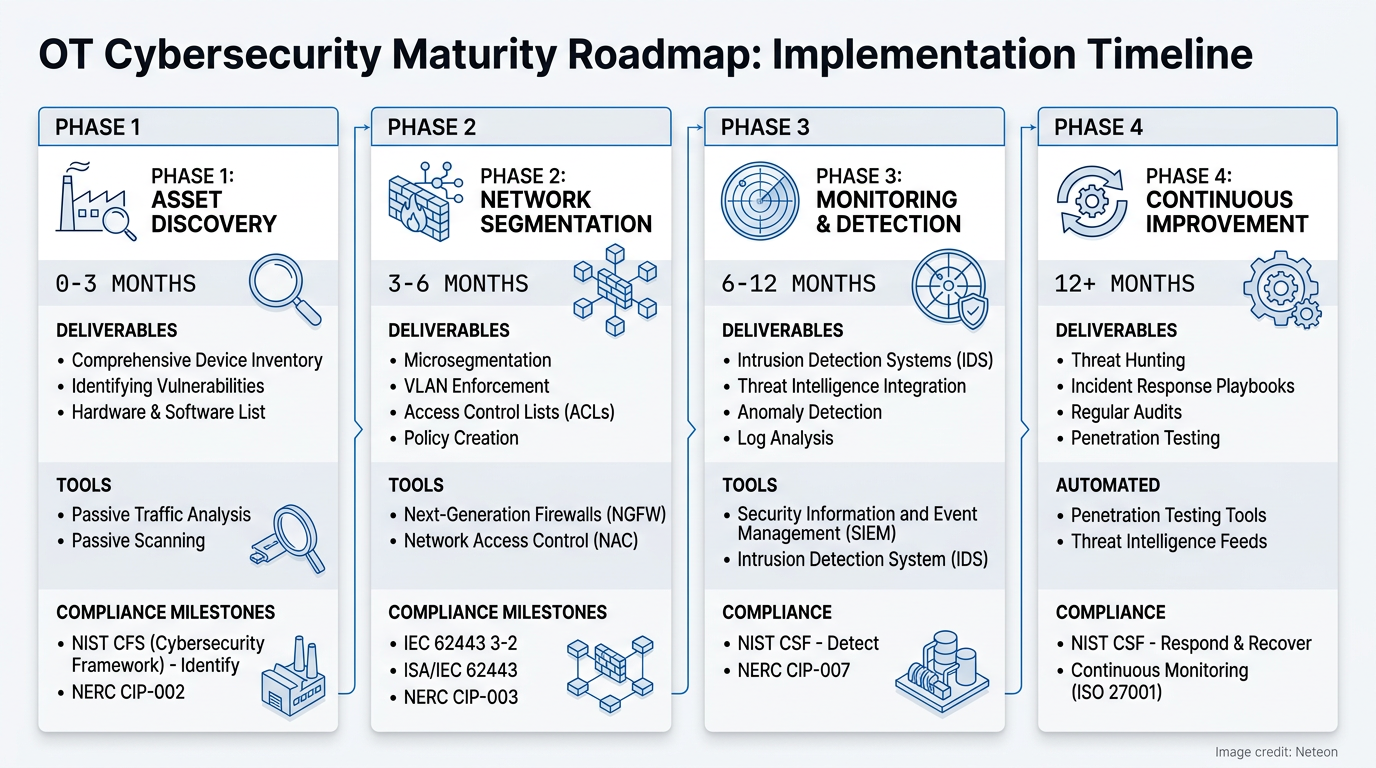
Implementation Roadmap
| Phase | Timeline | Activities | Deliverables |
|---|---|---|---|
| 1: Discover | Months 0-3 | Asset inventory, network mapping, risk assessment | OT asset database, network diagrams, risk register |
| 2: Segment | Months 3-6 | VLAN design, firewall deployment, access control | Zone architecture, firewall policies, ACLs |
| 3: Monitor | Months 6-12 | Deploy monitoring, establish baselines, SIEM integration | Alert playbooks, baseline profiles, SOC integration |
| 4: Mature | Months 12+ | Continuous improvement, advanced analytics, compliance | Audit reports, maturity scores, training programs |
Cybersecurity & Reliability
| Security Control | NIST Function | Moxa Solution | IEC 62443 Mapping |
|---|---|---|---|
| Asset Discovery | Identify | MXview One | FR 1 (Identification) |
| Network Segmentation | Protect | EDR-G9010, EDS managed switches | FR 5 (Restricted Data Flow) |
| Protocol Monitoring | Detect | MXview One + SIEM | FR 6 (Timely Response) |
| Zone Isolation | Respond | EDR-G9010 firewall rules | FR 5 (Restricted Data Flow) |
| Network Redundancy | Recover | Turbo Ring, RSTP | Availability (SL targets) |
Related Products
Product cards auto-generated by shopmoxa_scraper.py
Conclusion
Implementing NIST CSF in OT environments is a phased journey, not a one-time project. Starting with asset discovery (you cannot protect what you cannot see) and progressively building segmentation, monitoring, and response capabilities creates a sustainable security posture. Contact Neteon's engineering team for assistance designing your OT security architecture or conducting a network assessment.
Frequently Asked Questions
Q: Is NIST CSF mandatory for industrial organizations? A: NIST CSF is voluntary for most industries but is increasingly referenced by sector-specific regulations. Federal contractors, critical infrastructure operators under CISA guidance, and organizations seeking cyber insurance often find NIST CSF alignment essential.
Q: How long does a full NIST CSF implementation take for OT? A: A phased implementation typically takes 12-18 months to reach operational maturity. Phase 1 (asset discovery) can be completed in 90 days and provides immediate security value by identifying unknown connected devices.
Q: Can NIST CSF and IEC 62443 be used together? A: Yes — they are complementary. NIST CSF provides the organizational risk management framework, while IEC 62443 provides detailed technical controls. Many organizations use NIST CSF for governance and IEC 62443 for engineering implementation.
Q: What is the first step in implementing NIST CSF for OT? A: Asset discovery. Deploy passive network monitoring to build a complete inventory of all connected OT devices. This reveals unknown connections, shadow IT devices, and legacy systems that represent the highest risk.
Q: How does NIST CSF 2.0 differ from version 1.1 for OT? A: CSF 2.0 adds a sixth function (Govern) for organizational oversight, expands supply chain risk management guidance, and explicitly addresses OT/ICS environments. It also improves alignment with IEC 62443 and NIST SP 800-82 Rev 3.






