TL;DR
IT and OT security have fundamentally different priorities, device lifecycles, and threat models. Applying IT security practices directly to operational technology environments causes downtime, protocol conflicts, and compliance failures. This guide explains the key differences and outlines a practical convergence strategy using industrial-grade security appliances.
Why IT Security Practices Fail in OT Environments
Manufacturing and critical infrastructure operators face a growing dilemma: cybersecurity threats are increasing, but traditional IT security tools often do more harm than good when deployed on the factory floor. The root cause is a fundamental misalignment between IT and OT priorities.
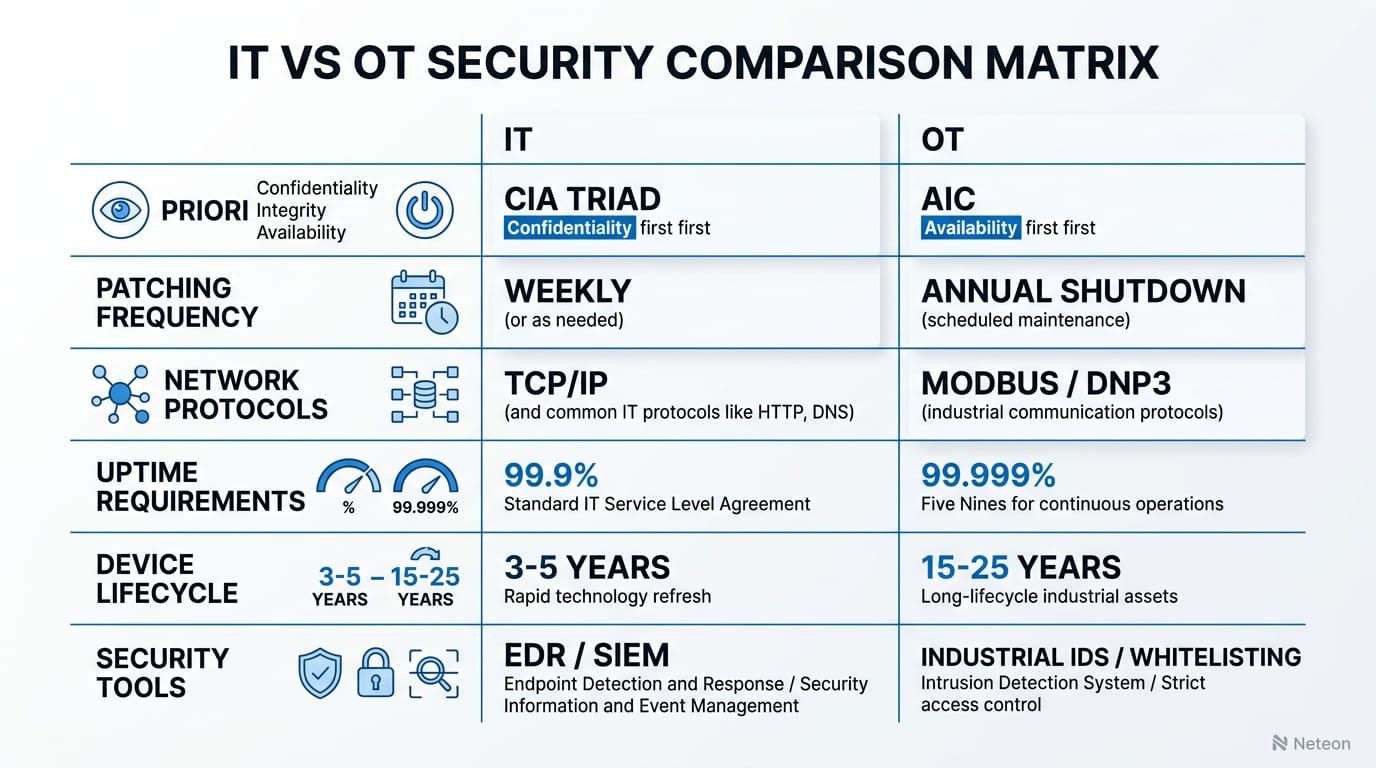
In IT, the CIA triad (Confidentiality, Integrity, Availability) prioritizes data confidentiality. In OT, the order reverses to AIC — Availability first, then Integrity, then Confidentiality. A 30-second network scan that would be routine in IT can crash a PLC controlling a chemical reactor.
| Parameter | IT Environment | OT Environment |
|---|---|---|
| Top Priority | Confidentiality | Availability (uptime) |
| Patching Cycle | Weekly/monthly | Annual shutdown windows |
| Device Lifecycle | 3-5 years | 15-25 years |
| Protocols | HTTP, TLS, SSH | Modbus TCP, DNP3, EtherNet/IP |
| Downtime Tolerance | Minutes acceptable | Seconds = production loss |
| Operating Temp | 0°C to 40°C (data center) | -40°C to 75°C (field) |
The Challenge: Legacy Devices Meet Modern Threats
Most OT environments run a mix of decades-old PLCs, RTUs, and HMIs alongside modern IP-connected sensors. These legacy devices:
- Lack authentication mechanisms (Modbus has zero built-in security)
- Cannot run endpoint protection agents
- Crash when subjected to active network scanning
- Use proprietary protocols that IT firewalls cannot inspect
A 2025 Dragos report found that 87% of industrial ransomware incidents originated from IT-OT boundary failures — attackers moving laterally from the enterprise network into unprotected OT segments.
The challenge is compounded by convergence: organizations connecting previously air-gapped OT networks to IT systems for data analytics and remote monitoring. Without proper segmentation, this creates direct attack paths to critical infrastructure.
The Solution: Industrial-Grade Security Architecture
Effective OT security requires purpose-built tools that understand industrial protocols and prioritize availability. The recommended approach follows IEC 62443 zone-and-conduit principles:
1. Network Segmentation with Industrial Firewalls
The Moxa EDR-G9010 Series industrial secure routers provide zone-based segmentation specifically designed for OT:
| Feature | Specification | Benefit |
|---|---|---|
| DPI for OT Protocols | Modbus TCP, DNP3, EtherNet/IP, IEC 61850 MMS | Inspects industrial traffic without disruption |
| IEC 62443-4-2 Certified | SL2 security level | Meets industrial cybersecurity standards |
| Operating Temperature | -40°C to 75°C | Deploys in harsh field environments |
| Failover Mode | Hardware bypass on power failure | Network stays operational during device failure |
| VPN Throughput | Up to 500 Mbps IPsec | Secure remote access without latency issues |
2. OT-Aware Network Monitoring
Unlike IT intrusion detection systems that generate false positives from industrial protocols, OT-specific monitoring tools like MXview One provide:
- Passive network discovery (no active scanning that disrupts PLCs)
- Protocol-aware anomaly detection for Modbus, DNP3, and OPC UA
- Automated asset inventory for devices that cannot run agents
- Real-time topology visualization with alarm correlation
| Metric | Before (IT Tools in OT) | After (OT-Native Tools) | Improvement |
|---|---|---|---|
| False Positive Rate | 340 alerts/day | 12 alerts/day | 96% reduction |
| Asset Visibility | 45% of OT devices | 98% of OT devices | +53 percentage points |
| Mean Time to Detect | 72 hours | 4.2 hours | 94% faster |
| Unplanned Downtime | 18 hours/month | 2.1 hours/month | 88% reduction |
Cybersecurity & Reliability
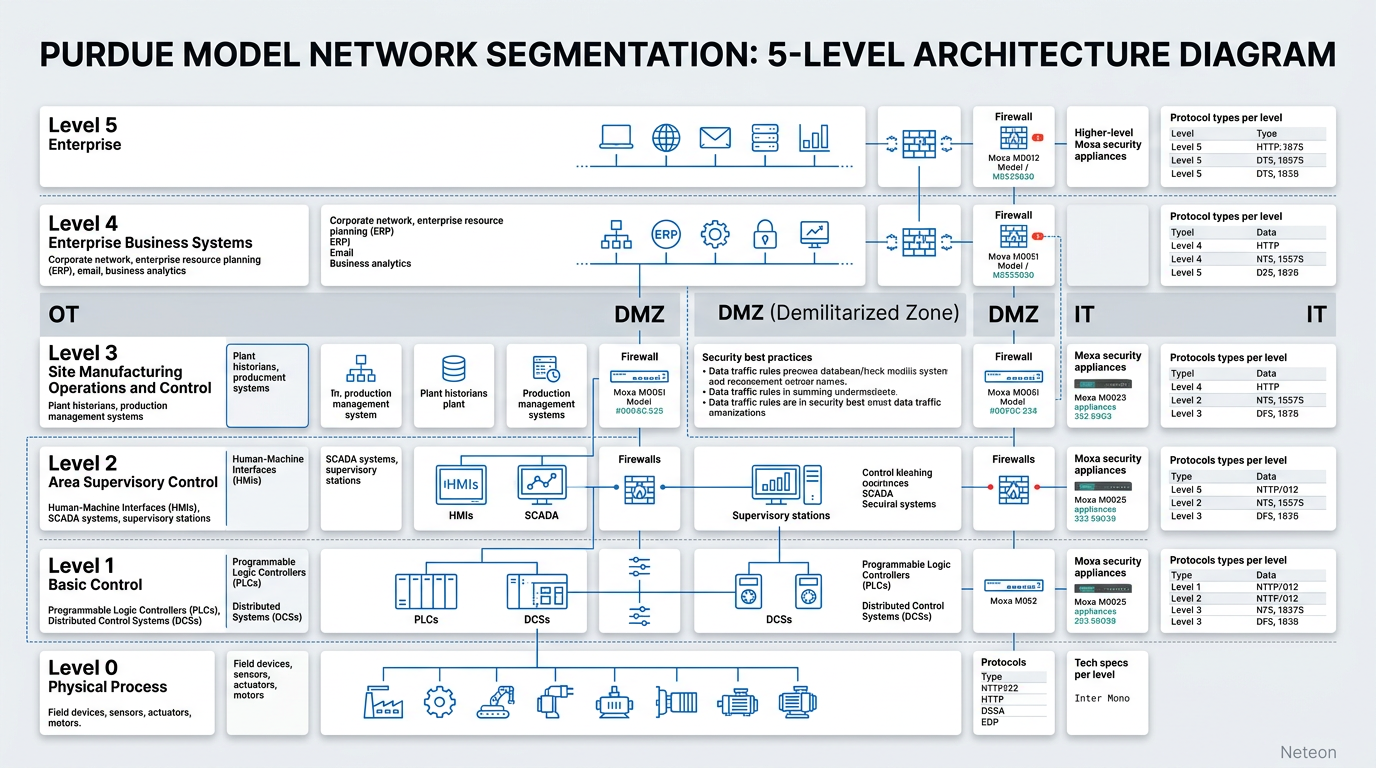
Building defense-in-depth for OT requires layered security at every level of the Purdue Model:
| Security Layer | Implementation | Standard |
|---|---|---|
| Perimeter | EDR-G9010 firewall/VPN at IT-OT boundary | IEC 62443-3-3 |
| Network | VLAN segmentation on managed switches | IEEE 802.1Q |
| Device | Port security, MAC filtering, 802.1X | IEC 62443-4-2 |
| Application | OT protocol whitelisting (DPI) | NIST SP 800-82 |
| Monitoring | MXview One passive network surveillance | IEC 62443-2-4 |
Reliability specifications: - MTBF: >500,000 hours for EDR-G9010 - Failover: <50ms with Turbo Ring redundancy protocol - Certifications: IEC 61850-3, IEEE 1613, NIST SP 800-82 aligned
Related Products
Product cards auto-generated by shopmoxa_scraper.py
Conclusion
The IT/OT security gap is not about technology maturity — it is about fundamentally different operational requirements. Organizations that deploy IT security tools in OT environments risk availability, compliance, and safety. Purpose-built industrial security appliances like the Moxa EDR Series bridge this gap by combining deep packet inspection for OT protocols with the ruggedness and failover capabilities that industrial environments demand.
For network architecture guidance or to evaluate industrial security solutions for your facility, contact our engineering team at shopmoxa.neteon.net/contact.
Frequently Asked Questions
Q: Can I use enterprise IT firewalls in OT environments? A: Enterprise firewalls lack OT protocol awareness (Modbus, DNP3, EtherNet/IP DPI) and do not meet industrial environmental ratings (-40°C to 75°C). They also lack hardware bypass failover, meaning a firewall failure takes down the entire OT network segment.
Q: What is the Purdue Model and why does it matter for OT security? A: The Purdue Model defines five hierarchical levels (0-5) for industrial control system architecture. It establishes security zones and conduits per IEC 62443, ensuring that compromise of one level does not cascade to critical process control layers.
Q: How often should OT devices be patched? A: OT patching typically occurs during planned maintenance windows (quarterly to annually) due to uptime requirements. Between patches, compensating controls like network segmentation, protocol whitelisting, and virtual patching via industrial firewalls provide protection.
Q: What is IEC 62443 and is it mandatory? A: IEC 62443 is the international standard for industrial automation and control system (IACS) security. While not universally mandatory, it is increasingly required by sector-specific regulations (NERC CIP for power, FDA for pharma) and is considered the baseline for OT security best practices.
Q: How does Moxa EDR hardware bypass work? A: When the EDR-G9010 loses power or experiences a critical failure, its hardware bypass relay automatically connects the LAN ports directly, maintaining network continuity. This ensures OT availability is never compromised by a security device failure — a critical requirement that IT firewalls lack.






