TL;DR
IEC 62443 is the global standard for industrial automation and control system (IACS) cybersecurity. This checklist provides a practical, step-by-step guide for achieving compliance across network architecture, device hardening, access control, and monitoring — with specific tool and configuration recommendations for each requirement.
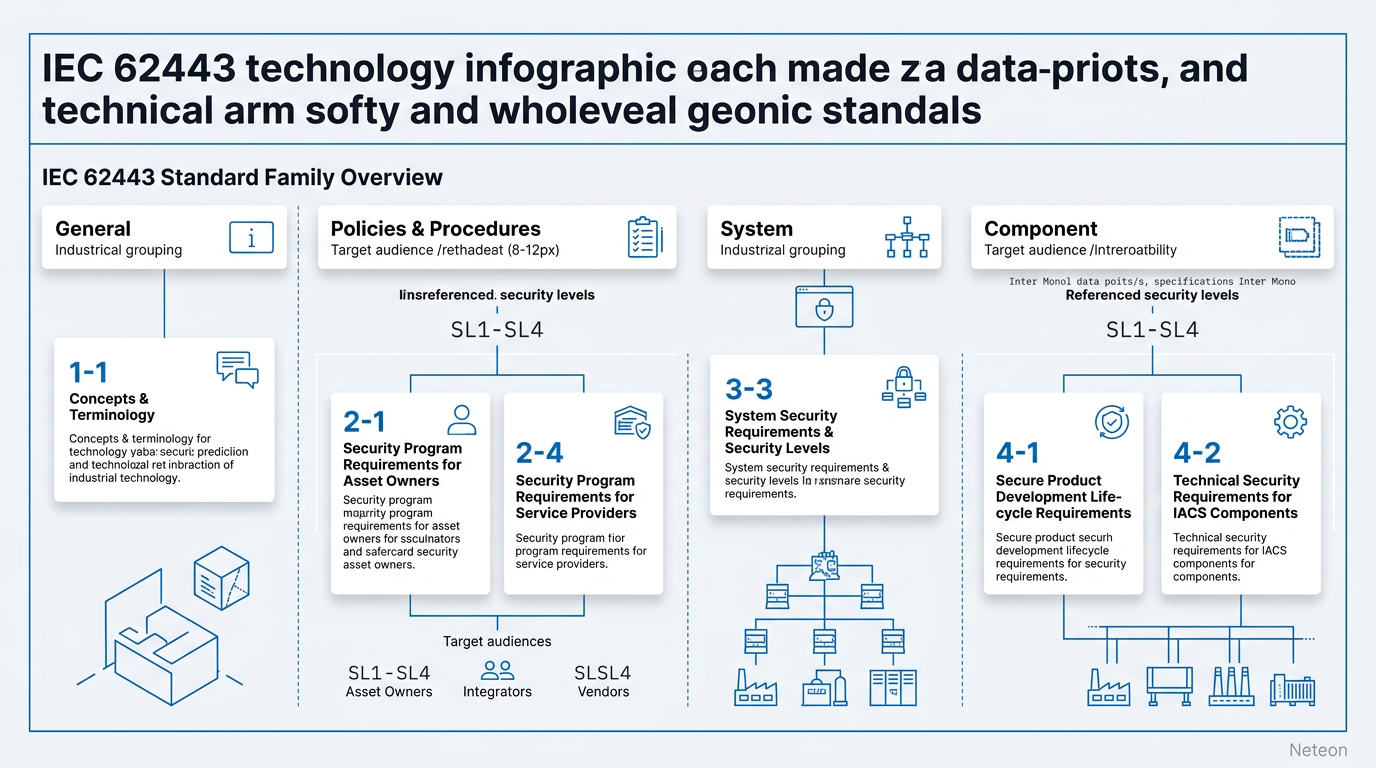
Understanding IEC 62443
IEC 62443 is a family of standards developed by ISA (International Society of Automation) and adopted by IEC (International Electrotechnical Commission). Unlike single-document standards, IEC 62443 is organized into four series addressing different stakeholders:
| Series | Focus | Target Audience |
|---|---|---|
| 62443-1-x | General concepts, terminology | All stakeholders |
| 62443-2-x | Policies and procedures | Asset owners, operators |
| 62443-3-x | System security requirements | System integrators |
| 62443-4-x | Component security requirements | Product vendors |
Security Levels (SL) define the rigor of protection:
| Level | Threat Actor | Example Environment |
|---|---|---|
| SL 1 | Casual or coincidental | Office network adjacent to OT |
| SL 2 | Intentional, low resources | Standard manufacturing |
| SL 3 | Sophisticated, moderate resources | Critical infrastructure, utilities |
| SL 4 | State-sponsored, extensive resources | National defense, nuclear |
Compliance Checklist: Network Architecture (62443-3-3)
Zone and Conduit Design:
- [ ] Define security zones based on criticality and function
- [ ] Establish conduits (controlled communication paths) between zones
- [ ] Deploy industrial firewalls at every zone boundary
- [ ] Document all inter-zone data flows and protocols
- [ ] Implement DMZ between enterprise IT and OT networks
Network Segmentation Implementation:
| Requirement | Implementation | Verification |
|---|---|---|
| Zone isolation | VLAN per zone on managed switches | Inter-VLAN traffic blocked by default |
| Conduit control | EDR-G9010 firewall rules per conduit | Only approved protocols/ports pass |
| Redundancy | Turbo Ring for network resilience | <50ms failover verified |
| DMZ | Dual-firewall DMZ architecture | No direct IT-to-OT paths |
Compliance Checklist: Access Control (62443-3-3 FR 1-2)
Foundational Requirement 1 — Identification and Authentication:
- [ ] Unique user accounts for all personnel (no shared logins)
- [ ] Role-based access control (RBAC) configured on all network devices
- [ ] Multi-factor authentication for remote access connections
- [ ] Account lockout after 5 failed attempts
- [ ] Automated session timeout for inactive connections (15 min default)
Foundational Requirement 2 — Use Control:
- [ ] Least privilege principle: users access only required zones/devices
- [ ] Separate accounts for administrative and operational functions
- [ ] Privileged access management for engineering workstations
- [ ] Vendor/contractor access limited to specific time windows
Compliance Checklist: System Integrity (62443-3-3 FR 3-4)
- [ ] Firmware integrity verification before deployment (cryptographic hash)
- [ ] Secure boot enabled on all supporting devices
- [ ] Configuration backup automated and stored offline
- [ ] Change management process for all OT device configurations
- [ ] Software whitelisting on HMIs and engineering workstations
Compliance Checklist: Data Confidentiality (62443-3-3 FR 4)
- [ ] Encrypted communication for all remote access (IPsec VPN minimum)
- [ ] TLS/SSL for web-based management interfaces
- [ ] SNMPv3 (encrypted) replacing SNMPv1/v2c on all managed devices
- [ ] Secure protocols for data historian communication
Compliance Checklist: Monitoring and Logging (62443-3-3 FR 6)
- [ ] Continuous network monitoring deployed across all zones
- [ ] Security event logging enabled on firewalls, switches, and gateways
- [ ] Centralized log collection with tamper-proof storage
- [ ] Automated alerting for unauthorized access attempts and policy violations
- [ ] Regular log review procedures (minimum weekly for critical zones)
| Monitoring Requirement | Tool | Configuration |
|---|---|---|
| Network topology | MXview One | Auto-discovery, SNMP polling |
| Traffic analysis | EDR-G9010 DPI logs | Protocol-specific rule logging |
| Device health | Managed switch SNMP traps | Port status, temperature, PoE |
| Access audit | RADIUS/TACACS+ | Centralized authentication logs |
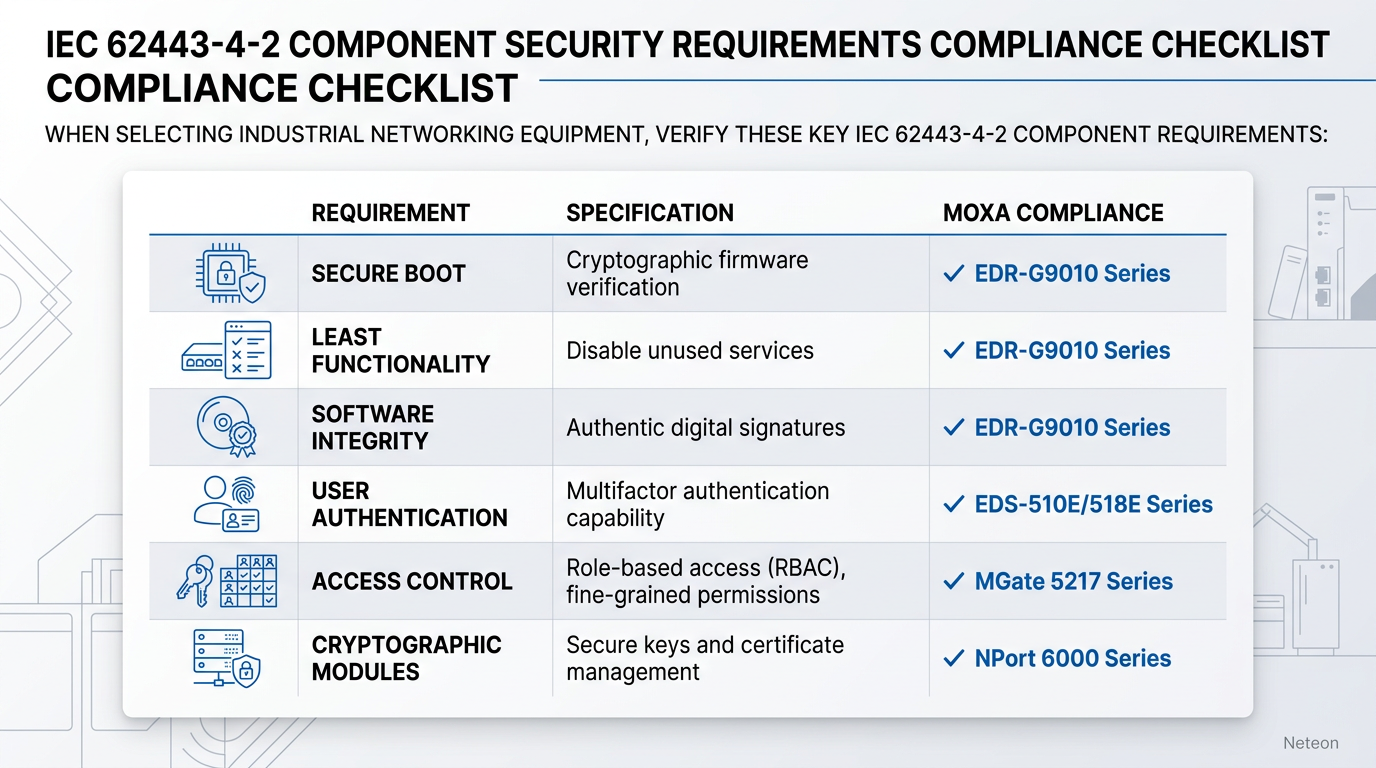
Compliance Checklist: Component Security (62443-4-2)
When selecting industrial networking equipment, verify these IEC 62443-4-2 component requirements:
| Requirement | Specification | Moxa Compliance |
|---|---|---|
| Secure boot | Cryptographic firmware verification | ✓ EDR-G9010 Series |
| Least functionality | Disable unused services/ports | ✓ All managed switches |
| Authentication | Local + RADIUS/TACACS+ | ✓ EDS/IKS managed series |
| Audit logging | Event logs with timestamps | ✓ All managed devices |
| Communication integrity | TLS, SSH, SNMPv3 | ✓ All managed devices |
Cybersecurity & Reliability
| Security Layer | IEC 62443 FR | Implementation |
|---|---|---|
| Network | FR 5 (Restricted Data Flow) | Zone/conduit architecture with EDR firewalls |
| Access | FR 1-2 (Auth + Use Control) | RBAC, MFA, RADIUS on managed switches |
| Integrity | FR 3 (System Integrity) | Secure boot, firmware verification |
| Monitoring | FR 6 (Timely Response) | MXview One, centralized logging |
| Availability | SL Targets | Turbo Ring redundancy, hardware bypass |
Related Products
Product cards auto-generated by shopmoxa_scraper.py
Conclusion
IEC 62443 compliance is achievable through systematic implementation of zone-and-conduit architecture, role-based access control, and continuous monitoring. Start with a gap assessment against your target security level, then prioritize network segmentation as the highest-impact control. For IEC 62443 gap assessments or network architecture design assistance, contact Neteon's industrial security team.
Frequently Asked Questions
Q: Is IEC 62443 certification mandatory? A: Certification is not universally mandatory but is increasingly required by procurement specifications in power (NERC CIP references it), oil and gas, and government contracts. Many asset owners require IEC 62443-4-2 certified components.
Q: What security level should my facility target? A: Most manufacturing facilities target SL 2 (protection against intentional attacks with low resources). Critical infrastructure (power grids, water treatment) should target SL 3. SL 4 is typically reserved for national security applications.
Q: How long does IEC 62443 compliance take? A: Initial compliance for a medium-sized facility typically takes 6-12 months for SL 2 and 12-24 months for SL 3, depending on the baseline maturity of existing OT security controls.
Q: Can I achieve IEC 62443 compliance without replacing legacy equipment? A: Yes. Compensating controls like network segmentation, industrial firewalls with DPI, and monitoring can protect legacy zones. The firewall becomes the security boundary, allowing non-compliant devices to operate within a protected zone.
Q: What is the difference between IEC 62443 and NIST SP 800-82? A: IEC 62443 is an international standard with certification programs and specific security levels. NIST SP 800-82 is US-government guidance for ICS security. They are complementary — NIST 800-82 Rev 3 explicitly maps to IEC 62443 requirements.






